Products
Buy options
2.33 USDPlease check product and platform compatibility before placing an order
All pictures shown are for illustration purpose only. Actual product may slightly vary due to product enhancement or other reasons.
Leather Case for Token2 Dual Interface FIDO2 Security Keys
Protect your key while keeping it fully usable.
We do not recommend attaching the Token2 key directly to a keyring, as the body is made of plastic and may wear or break over time. This custom-fit leather case adds a layer of protection and durability, making it easier and safer to carry your key every day.
- Designed for Token2 Dual Interface FIDO2 keys (USB-A & USB-C)
- Expose either USB-A or USB-C depending on your preference
- Touch sensor accessible – use the key without removing it
- Snap button and keyring loop for convenient everyday use
- Made from stitched black leather with a simple, functional design
Does not support dual-interface biometric keys.
Related products
PIN+ Dual Octo Release3.3 FIDO2.1 Security Key - Nonbranded
PIN+ Dual Octo Release3.3 FIDO2.1 Securi...
OrderPIN+ Dual Release3.3 - FIDO2.1 Key with PIV, OpenPGP and OTP and Dual USB Ports
PIN+ Dual Release3.3 - FIDO2.1 Key with ...
OrderBlog
04-04-2026
Understanding FIDO User Verification Modes and the always_uv Setting
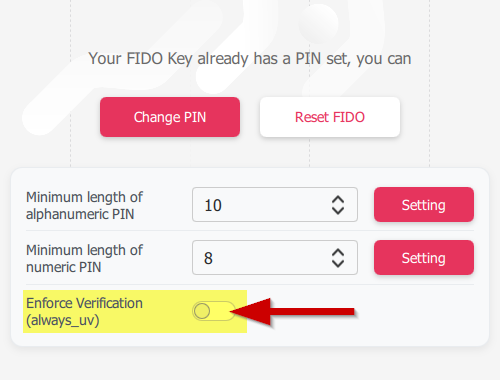 Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
05-03-2026
Introducing TOTPVault — self-hosted TOTP management for teams
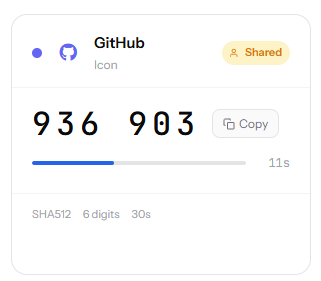 Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
21-12-2025
Android, NFC, and the Missing Piece of WebAuthn
 For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.






